
The internet is a vast landscape, commonly divided into three distinct layers: the surface web, deep web, and dark web. While most users navigate the surface web with ease, access to the dark web remains a topic shrouded in mystery and misunderstanding. This article aims to demystify the dark web, exploring its purpose, how to access it safely, and important considerations for users who want to delve deeper into this hidden part of the internet.
- Access to the deep web requires special authorisations, authentication or the use of special software such as the Tor network.
- Dissidents in restrictive regimes may need anonymity in order to safely let the world know what’s happening in their country.
- The dark web is shrouded in mystery, but not every onion website is dangerous.
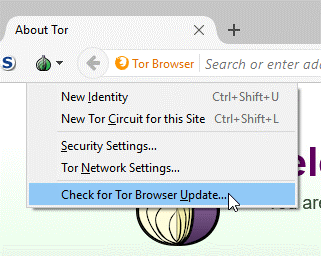
- While some can simply install and use the Tor browser like any other, there are a few complications for those in countries where Tor is blocked, on corporate or university networks where it's banned, or where more security is needed.
- Note that Hidden Wiki links sometimes lead to unsafe content, so be wary about what you click.
Gain insight through actionable threat intelligence and expert analysis. Read how our customers solve their most pressing cybersecurity challenges Check out our side-by-side comparison of Proofpoint vs. competitors. Strengthen your business with enterprise-grade security built to grow with you. Protect your institution while meeting regulatory and compliance requirements. Deliver secure, high-performance email protection for your networks and customers with Cloudmark.
Access To The Dark Web
Many of these illegal activities use Bitcoin and other cryptocurrencies for transactions so that the sellers and buyers can remain anonymous. The protections afforded people looking to be anonymous for legitimate reasons also provide the same anonymity for cybercriminals and criminals operating in the real world who desire private communications. In fact, it can often be much safer for people in such circumstances to use the Dark Web over a virtual private network (VPN). The Dark Web is used by cybercriminals to buy and sell illegal goods and services, coordinate attacks, distribute malware and phishing kits, and share other prebuilt exploits. This is where things might get just a bit confusing, as the Dark Web is nearly synonymous with illegal activity.
The dark web is a segment of the internet that is not indexed by traditional search engines. To access this hidden layer, users typically require specific software, configurations, or authorization. The most notable platform for gaining access to the dark web is Tor, which stands for “The Onion Router.” Tor enables users to browse the internet anonymously, helping protect their privacy while accessing various websites that operate outside of the reach of conventional internet protocols.
What is Tor?
Tor is a free software used for enabling anonymous communication. It redirects traffic through a network of servers, preserving user privacy by obscuring their IP addresses. To access the dark web via Tor, users need to download the Tor Browser, which is specifically designed to navigate .onion sites—websites that exist only within the Tor network.
- To this day, Tor is still the favored route of access to the dark web.
- RussianMarket specializes in the sale of “logs”, CVVs, dumps and RDP access.
- Hence, the deep web encompasses the dark web which constitutes a relatively smaller section entirely hidden and requires software specialized as Tor to access.
- While the dark web is often linked to illegal activity, it also serves important legitimate purposes.
- Understanding the distinctions between the dark web and the deep web environments is essential for developing effective cybersecurity strategies.
- While the Tor browser boosts privacy, pairing it with a VPN adds a critical layer of security.
How to Access the Dark Web
- Step 1: Download the Tor Browser from the official Tor Project website. Ensure you are using a secure and trusted source to avoid malicious software.
- Step 2: Install the Tor Browser on your device and open it. The browser will connect to the Tor network, providing you with anonymity.
- Step 3: Use search engines designed for the dark web, such as DuckDuckGo's .onion version, to explore available content. Note that navigating the dark web involves risks—proceed with caution.
Understanding the Risks

While access to the dark web can provide valuable resources and information, it also comes with significant risks. Many sites on the dark web offer illegal products and services, and users can encounter scams or harmful content. It is crucial to prioritize cybersecurity and be mindful of the laws in your jurisdiction. Always use a Virtual Private Network (VPN) for an added layer of security when browsing.
Legitimate Uses of the Dark Web
Despite its notorious reputation, the dark web can also serve legitimate purposes. Journalists, activists, and whistleblowers often use dark web platforms to exchange information without fear of censorship or persecution. It provides a vital space for free expression, particularly in countries with strict internet regulations.
Conclusion
Gaining access to the dark web is a straightforward process, yet it requires a careful approach to ensure user safety and legality. Understanding the tools needed and the potential risks involved is essential for anyone interested in exploring this hidden side of the internet. By remaining informed and cautious, users can navigate the dark web responsibly and possibly uncover valuable resources that promote informed discussions and awareness.



