Investigators should assume attribution risk exists and rely on isolation, policy, and auditing rather than personal devices or consumer VPNs. Investigators should avoid transacting, engaging, or downloading from illicit markets and use isolated, non-attributable browsing with audit logs. There are security controls in place and built-in auditing. It also means the ability to manage attribution so angry site admins don't track a researcher back to their real-life persona, and protection from easy-to-click malware. Maintain a complete record of activities while on the dark web and have a policy in place for “rules of engagement” when on sites where criminal activity may occur.
The .onion dark web is often shrouded in mystery and misconceptions, making it a topic of intrigue for many. Understanding the .onion network is essential for those interested in digital privacy, cybersecurity, and the complexities of the internet. This article aims to demystify the .onion dark web, highlighting its structure, potential uses, and inherent risks. As more people venture into this hidden digital space, knowledge becomes a vital tool for both safety and awareness.
Inbound link analysis of a select set of sites that we view as top-tier confirmed that they do indeed have less visibility, measured by a reduced number of links pointing to them. Its 8,400 live onion domains are a tiny fraction of the surface web, with only 15% being live out of a mere 55,000 onion sites total. The contents of all live onion pages scraped with the spider are added to the Recorded Future® Platform. In 2015, Deep Dot Web reported having to aggressively shut down fake copies of their onion site that had the onion urls of popular markets replaced by phishing links.
This method is called Tor over VPN, and it’s a great way to increase your privacy over using Tor alone. Needless to say, we don’t condone any content forbidden by law. Naturally, this makes the dark web a breeding ground for illegal activity. With the above dangers, it’s imperative to tread carefully as you step into the dark web.
.onion Dark Web
The .onion domain is part of the Tor network, which provides anonymous communication and access for its users. At its core, the Tor network allows individuals to browse the internet without revealing their identity or location. When someone accesses a .onion site, they are utilizing a specific type of URL that is only reachable through the Tor browser, designed to protect user anonymity through layered encryption.
- In practice, your Tor Browser first encrypts data for the final server, then again for a middle node, and again for an entry guard node.
- But I will never know because it’s gone now.
- Their crawlers do not index .onion domains or any content on the Tor network.
- Dark web marketplaces offer mostly illegal products and services in exchange for payment.
- Silo for Research gives investigators anonymous, secure access to Tor in one click.
How the .onion Network Works
The infrastructure of the .onion dark web includes a series of relays operated by volunteers around the globe. When a user sends a request, it is encrypted multiple times and routed through several random relays before reaching its destination, effectively concealing the user's IP address. This technology not only protects users from potential surveillance but also enables access to websites that may be blocked or censored in certain regions.
Accessing .onion Sites
To explore the .onion dark web, users must download the Tor browser, which is specially designed to handle .onion URLs. Unlike standard web browsers, the Tor browser allows users to visit sites that would otherwise remain hidden from the public internet. It's important to note that while there are legitimate uses for the .onion network—including protecting free speech and journalism—there are also illegal activities that occur within this space that pose risks to users.
Legitimate Uses of the .onion Dark Web
The .onion dark web is not solely a hub for illicit activities; it also serves valuable purposes. Whistleblowers, journalists, and activists often rely on .onion sites to communicate securely and anonymously, especially in oppressive regimes where freedom of speech is curtailed. These platforms can facilitate the sharing of information, allowing individuals to uncover corruption and human rights abuses without fear of reprisal.
Risks Associated with the .onion Dark Web
While the .onion dark web can offer anonymity and privacy, it is not without its dangers. Users may encounter scams, malicious software, and illegal content that could lead to severe legal consequences. The lack of regulation on these hidden sites makes it essential for users to exercise caution and be aware of potential threats. Engaging with any entity on the dark web necessitates a keen awareness of the risks involved, as well as a commitment to maintaining personal safety and security.
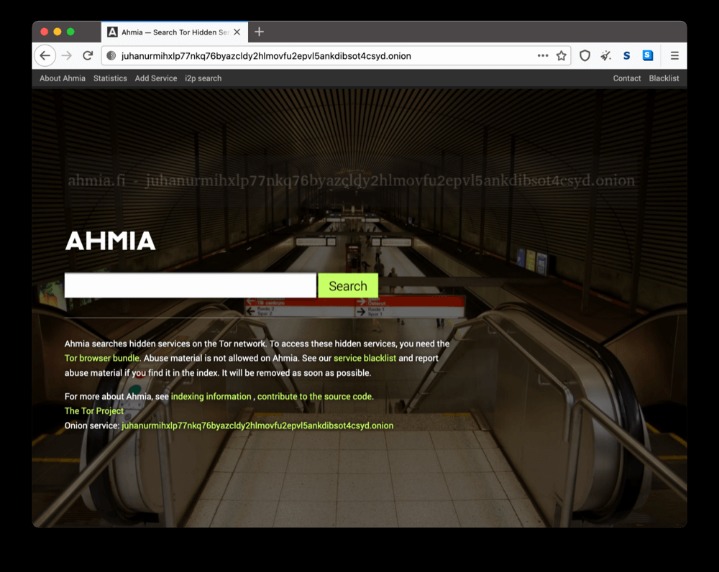
- Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found.
- This is a huge risk, as the Tor Browser disables JavaScript by default to protect users from being "fingerprinted" or de-anonymized.
- They do so to avoid the usual tracking and surveillance found on the regular internet.
- Spear Phishing threats are rising as the data on the dark web expands.
- You can visit an onion website or an .onion link by simply going to our home page and selecting the Tor browser.
Conclusion
In summary, the .onion dark web is a complex and multifaceted part of the internet that requires a nuanced understanding. While it offers opportunities for privacy and secure communication, individuals must approach it with caution and awareness of its associated risks. Education about the .onion dark web empowers users to navigate digital landscapes safely, whether for legitimate purposes or otherwise. Staying informed is the first step towards ensuring safety and adopting best practices while exploring this hidden side of the online world.