
The internet is a vast expanse of information, but not all of it resides in easily accessible places. Beneath the surface lies a hidden realm known as the dark web, where anonymity reigns and the rules of the conventional internet often do not apply. Understanding how to access the dark web can be beneficial for various reasons, from safeguarding personal privacy to researching topics not typically covered in mainstream media. This article aims to guide you through the essentials of navigating this obscure segment of the online world safely and responsibly.
Accessing The Dark Web
There are numerous phishing sites, too, as explained earlier, designed to fool users into giving up their personal data. However, remember to be cautious when accessing this hidden part of the internet. Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it. Many cybersecurity and tech experts recommend using a VPN whenever you want to access the dark web via the Tor Browser or any other specialist browser. Given the many cyber threats present on the dark web, it’s recommended to be extra careful when you access it.
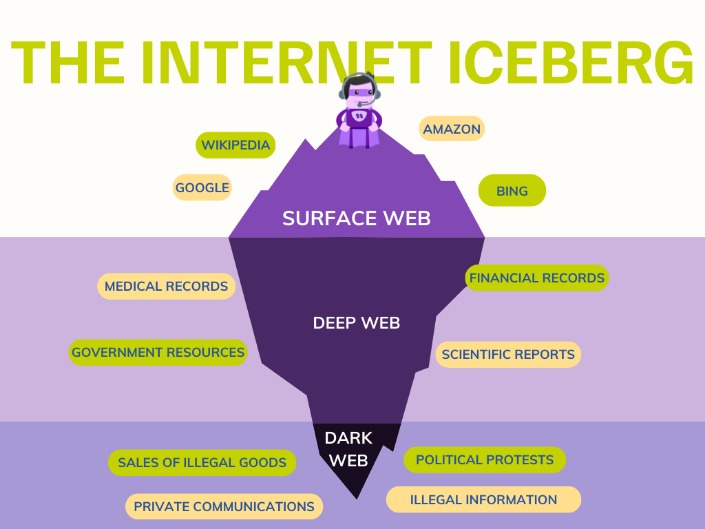
Before diving into how one may access the dark web, it's crucial to understand what it is. The dark web is part of the deep web, which encompasses all parts of the internet not indexed by traditional search engines like Google or Bing. While the deep web includes benign items such as databases or private websites, the dark web is often associated with illicit activities, making it a mystery to many.
The Basics of Dark Web Access
Identities and locations of darknet users stay anonymous and cannot be tracked due to the layered encryption system. Tor browsers create encrypted entry points and pathways for the user, allowing their dark web searches and actions to be anonymous. The darknets which constitute the dark web include small, friend-to-friend networks, as well as large, popular networks such as Tor, Hyphanet, I2P, and Riffle operated by public organizations and individuals. Through the dark web, private computer networks can communicate and conduct business anonymously without divulging identifying information, such as a user's location.
To access the dark web, users typically employ special software that anonymizes their identity and browsing activity. The most commonly used tool for this purpose is Tor (The Onion Router), which allows users to visit sites ending in a “.onion” domain. Here are the steps to access the dark web safely:
- By downloading the Tor browser from its official website, individuals are able to navigate using.onion URLs that connect them to concealed destinations within this part of the internet.
- The surface web represents only a small percentage of what’s available on the entire internet but is where most online activities occur.
- Each version of the dark web provides its own dataset, encryption services and risks from attempting to access it.
- Dark web monitoring is a core component of many threat intelligence efforts.
- The dark web A small subset of the deep web, the dark web requires a unique browser like Tor to gain access and browse the content.
- Download Tor Browser: Start by downloading the Tor Browser from its official website to ensure that you’re getting a secure version.
- Install with Caution: Follow the installation instructions, and make sure to enable security settings that best suit your activity.
- Connect to the Tor Network: Once installed, open the Tor Browser and click on “Connect” to access the Tor network.
- Know Where to Navigate: While using the Tor Browser, you can find dark web links through various forums or specialized websites that compile directories of .onion sites.
Safety Measures
- Dark web forums are online communities where individuals participate in discussions on a wide range of subjects, from technology and privacy to more illicit matters.
- Partner with us for network security tech integrations that boost your product’s capabilities and open new revenue channels.
- Users need special browsers, like Tor, to create secret tunnels for accessing it.
- Tor shares similarities with VPNs and proxy servers — all of these tools allow anonymous browsing.
When venturing into the dark web, it is imperative to prioritize safety and anonymity. Here are some essential tips:
- Don’t Share Personal Information: Always refrain from sharing your real identity, location, or any personal data.
- Utilize a VPN: Consider using a Virtual Private Network (VPN) in conjunction with Tor for an extra layer of security.
- Be Wary of Scams: The dark web is rife with scams and fraudulent offers; always exercise caution when navigating.
- Stick to Reputable Sources: Engage with well-known or recommended .onion websites to reduce risks.
Legal Considerations
It’s important to understand that while there are legal uses for the dark web, some activities may cross ethical and legal lines. Engaging in illegal transactions or accessing prohibited content can lead to serious consequences. Always consider the implications of your actions and make informed choices.
Potential Benefits of Accessing the Dark Web
Despite its notorious reputation, the dark web also serves valuable purposes. Journalists and activists often use it to communicate securely in oppressive regimes. It provides a platform for whistleblowers to expose wrongdoing anonymously. Researchers can also find data that isn't readily available on the surface web, making it a goldmine for certain inquiries.
Conclusion
In conclusion, accessing the dark web can be enlightening and empowering when approached with caution and responsibility. Whether for research, privacy, or activism, understanding how to navigate this obscure part of the internet is crucial in our digital age. Always prioritize safety and legality while exploring, and remember that knowledge is a powerful tool in making informed decisions.



